Why Phishing Looks Normal Today
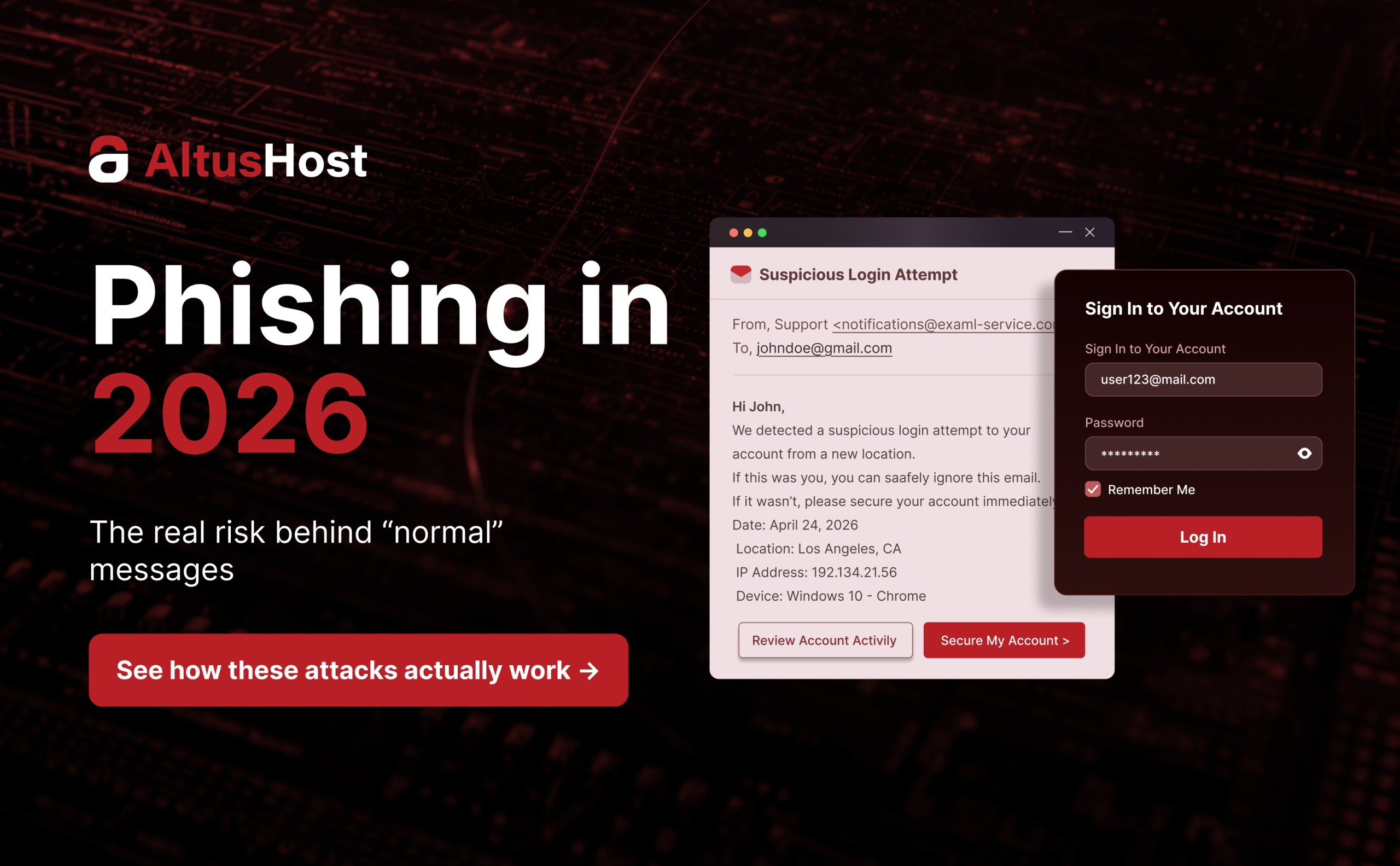
Most phishing attacks don’t start with something that looks suspicious.
They start with something that looks completely normal. Modern scams are no longer easy to spot and often
look completely legitimate. A login alert, a payment confirmation request, a delivery update, or a message that appears to come from someone inside your company.
There is no obvious red flag, no broken language, no strange formatting. The message fits into your day so naturally that you don’t question it. These attacks are a type of cyber fraud where attackers trick users into entering sensitive data on fake websites.
It looks normal, which is exactly the problem and the reason phishing works so effectively today. No longer based on poor imitations, phishing now blends seamlessly into legitimate communication.
The attacker’s goal is not to raise suspicion, but to remove it entirely.
When that happens, the difference between a real request and a malicious one becomes almost invisible.
Sometimes, that difference is only a single click.
How Phishing Attacks Actually Work
Phishing is often described as a cyberattack, but technically it is closer to manipulation than to intrusion.
Instead of breaking through security layers, the attacker convinces the user to open the door.
In practice, this means creating a scenario where the user voluntarily enters sensitive data such as login credentials, payment details, or verification codes on a controlled page that looks legitimate. Once that information is entered, access is no longer protected by systems, because it has been handed over.
This is what makes phishing fundamentally different from other types of attacks.
It does not depend on system vulnerabilities. It depends on predictable human behavior.
Phishing attempts continue to evolve precisely because human behavior remains consistent, which is why phishing protection cannot rely on a single layer of defense.
From Obvious Scams to Invisible Attacks
The biggest shift in phishing over the past decade is not just technical improvement, but strategic change.
Early phishing attempts were easy to detect because they relied on volume rather than precision.
Messages were generic, often poorly written, and sent to large numbers of users without context.
Today, that approach has been replaced with targeted execution. Attackers invest more effort into fewer messages, but those messages are significantly more effective.
Language is natural, formatting is clean, and the scenario is believable. In many cases, the message reflects something that could realistically happen at that exact moment. This shift has made phishing attempts less visible but far more dangerous.
Phishing attacks are becoming harder to detect.
Why Phishing Feels Legitimate
One of the key reasons phishing attacks succeed is that they mirror real processes.
A request to confirm a login attempt, verify a payment, or resolve an account issue is not unusual.
These are actions users perform regularly, which means they are less likely to question them.
Attackers build on that familiarity.
They replicate not only the visual design of trusted platforms but also their tone and communication structure.
This creates a situation where the user is not making a risky decision. They are simply continuing what feels like a normal process.That is the critical difference.
Phishing attacks no longer interrupt the user experience. They become part of it.
The Psychology Behind the Click
Phishing attacks are designed around reaction. The message is structured to create a sense of urgency or importance, pushing the user to act before fully evaluating the situation.
When a notification suggests that an account might be blocked or a payment might fail, the instinct is to resolve the issue immediately. In that moment, speed takes priority over verification. The user is not ignoring security. They are simply following what appears to be a logical next step.
That is exactly what the attacker relies on.
It is often assumed that only less experienced users fall for phishing attacks. In reality, well-designed phishing attacks affect experienced users as well.
The difference is rarely knowledge. It is timing and attention. A single moment of distraction is enough.
Phishing attacks do not succeed because users are careless. They succeed because they align with how users naturally respond.
Quick signs of phishing attacks
- urgency or pressure to act immediately
- domains that look similar but are not identical
- requests for login credentials, payment details, or verification codes through a link
If a message combines urgency with a request for action, it is one of the clearest signs of a phishing attack.
What a Modern Phishing Attack Looks Like
A typical phishing attack today is structured to minimize doubt at every step.
Users receive messages that appear to come from a trusted service.
The content references a realistic situation, such as a login attempt or a transaction issue.
Then the link leads to a page that looks identical to the original platform, including branding, layout, and even interactive elements.
For example, a message from your bank asking you to confirm a transaction can look completely legitimate, especially if it includes familiar branding and timing that matches your recent activity.
The user enters their credentials and confirms a one-time code. At that point, the attacker uses the same data in real time to access the actual account. There is no delay, no warning, and no visible sign of compromise.
This entire process can be completed in under a minute, which is why phishing attacks are considered one of the fastest and most effective attack methods today. No warning, no second chance, one click is enough.
Where Businesses Are Most Exposed
For businesses, phishing attacks are not just a security concern. They represent a direct operational risk.
A compromised account can lead to unauthorized access, data leaks, and disruption of internal communication. In many cases, attackers do not stop at one account. They use it as an entry point to move deeper into the system. One of the most common scenarios involves impersonation. An attacker gains access to an internal email account and sends messages that appear to come from a colleague or manager.
These messages may request urgent payments, document access, or sensitive information.
Because the communication appears legitimate, the likelihood of compliance is high.
The consequences are not limited to financial loss. Phishing attacks can affect reputation, customer trust, and long-term stability. In some cases, the damage continues long after the initial breach.
Why Infrastructure Still Matters
User awareness is critical, but it is not sufficient on its own.
Even well-informed users can make mistakes, especially under pressure.
This is where infrastructure becomes essential.
A secure system should not rely entirely on user decisions. It should include mechanisms that detect unusual behavior, flag suspicious login attempts, and prevent unauthorized access. Without this layer, phishing protection becomes incomplete. This is why infrastructure and hosting-level protection matter.
Reliable hosting and properly configured environments play a key role in reducing exposure to phishing attacks.
Security is not only about preventing attacks, but also about limiting their impact when they occur.
What We do to Reduce Phishing Risk
Even with advanced infrastructure and built-in security layers, phishing attacks remain among the most common threats in modern hosting environments. Because of that, protection cannot rely on a single checkpoint.
While phishing attacks target users directly, infrastructure-level protection plays a critical role in limiting their impact. At AltusHost, security is integrated into the entire hosting stack.
Every account operates within an isolated environment powered by CloudLinux, which helps contain potential threats and prevents them from spreading across other accounts. In addition, Imunify360 continuously monitors and filters malicious activity at the server level.
All connections are secured through SSL encryption, ensuring that data exchanged between users and services remains protected. Combined with a DDoS-protected network and redundant infrastructure, this creates a stable and controlled environment for every login and interaction.
Daily backups add another layer of protection, enabling fast recovery in the event of a compromise or unexpected activity.
Security is not only about blocking phishing attacks. It is about reducing what an attacker can do if access is ever compromised.
Quick protection checklist
- Avoid clicking links in unsolicited messages
- access services directly through official domains
- Verify domain names carefully before entering data
- Never provide sensitive information under pressure
- double-check requests that involve payments or credentials
These steps may seem basic, but they significantly reduce the success rate of phishing attacks.
How to Reduce Exposure in Practice
Reducing phishing risk starts with small, consistent habits. Messages that require immediate action should always be treated with caution. Instead of following links, it is safer to access services directly through official websites, especially when dealing with sensitive information.
Even minor inconsistencies in domain names should not be ignored. At the same time, organizations need to ensure that their systems are properly configured and monitored. This includes access controls, authentication layers, and visibility into unusual activity.
Security is not a single action, but a continuous process that combines user behavior and system design. When these elements work together, the likelihood of a successful phishing attack decreases significantly. The next time you receive a message like this, pause before clicking.
What This Means Going Forward
Phishing attacks are not going away. In fact, phishing attacks are becoming more integrated into everyday digital communication. As messages become more convincing and attacks more precise, the ability to recognize phishing will continue to decrease.
The margin for error is smaller than ever. Phishing protection must evolve alongside the attacks themselves. That does not mean users are defenseless. It means the approach to protection has to change.
Instead of relying on obvious warning signs, the focus should shift to awareness, verification, and system-level protection. Understanding phishing attacks and how to recognize phishing is no longer optional. It is a basic requirement for operating safely in any digital environment.
The One Decision That Makes the Difference
Phishing attacks happen quickly, but the response does not have to.
The most effective defense is often the simplest one.
Take a moment before acting. Check the context. Verify the source.
The difference between a secure account and a compromised one is often just a few seconds.
Sometimes, it’s only a single click.